We’re pleased to welcome guest bloggers Wendy Betts and Raquel Vazquez Llorente here to share their insights on documentation apps and metadata for legal purposes. Wendy Betts is the Director of eyeWitness to Atrocities, an organization that combines legal and technological expertise to aid investigations and promote accountability for international crimes. Raquel Vazquez Llorente is the Senior Legal Advisor.
By Wendy Betts and Raquel Vazquez Llorente
In a series of previous blog posts on documenting during internet shutdowns, Yvonne Ng touched on questions around metadata collection and different apps available for activists, such as eyeWitness to Atrocities, ProofMode, Tella, and others. In the next two blog posts, we will dive deeper into metadata and the considerations you should keep in mind when evaluating and selecting which app is right for you, particularly in situations where you might not have reliable internet connection. (Part II: Understanding the limitations of metadata when it is used for legal purposes will be published next week.)
For human rights defenders and activists using photo and video to document abuses across the globe, metadata plays a crucial role in authenticating and verifying their footage for external audiences. As WITNESS has addressed, there are multiple apps that can be used for documenting human rights abuses, but not all will serve the same purpose. They may offer different functionality. They may also capture different metadata, and record these data points in varied ways.
When you are assessing which documentation app to use, it is important you fully understand the metadata collected by the app. This blog post outlines the questions we recommend you ask, either by testing the app or contacting the app provider.
How accurate is the data?
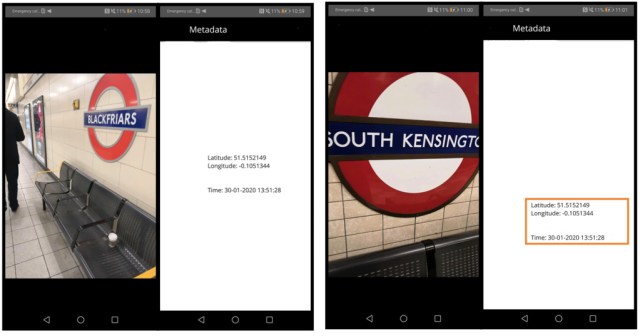
Not all metadata is created equal. Some metadata can be captured directly by the hardware sensors on the device. Other metadata is created by interpreting different data points taken from these sensors or from online sources. Location, for example, can be either recorded directly from the hardware sensors on the device or determined using information from the cell towers and wifi networks to which you are connected. Another example is altitude. Mobile phones do not have altimeters, so most phones calculate altitude by a combination of barometric pressure and GPS readings. While a barometer can give a measurement of the distance above sea level, the reading can change with atmospheric conditions, and the error can be tens of meters or more. As a result, photos of the same location taken with the same device could elicit different altitude readings.
Additionally, derivative metadata may not be calculated consistently across devices, making this information unhelpful for verifying your media and, in some instances, detrimental. For instance, certain phones may not support a barometer function and only use the GPS for measuring altitude (which may actually make this metadata more inaccurate). If you envision your media being used in future legal proceedings, relying on data points that are inconsistent may undermine the credibility of the rest of the metadata. More on this in Part II.

Another related consideration is to check whether the app is pulling metadata from the cache or memory of the device. This can happen when the hardware sensors cannot get a reading or the app is relying on your internet connection to look up data points and you are not online. Using information from the cache can be a problem because, for instance, if the app cannot get a GPS reading and instead pulls the last known location from the memory, the GPS reading could be miles away from your actual location. Or you could end up with two GPS readings, miles apart, for the same photo or video—which would wholly undermine the verification value of the metadata.
Before using a documentation app, you should check how the metadata is collected by the app, particularly if you are planning to document during an internet shutdown or you cannot rely on cell phone data. An easy way to test this would be to take a photo in a safe location with the app, then turn off all data and Wi-Fi and capture more test photos across different locations far enough apart for the GPS readings to be different. The GPS coordinates should not be the same, and they should match the actual location where you took the media. If the metadata is being pulled from the memory of the device, most likely you will find that some of the photos have the same or similar GPS coordinates to the first photo you took when you had a connection.
WITNESS tip: You can read an app’s documentation, contact the app developer, or run your own tests to find out whether the metadata in your documentation app is captured from the hardware sensors or by interpreting different data points. Choose apps that capture data accurately, particularly when capturing media offline. Also, film in ways that support the use of your video for legal purposes — check out the Video as Evidence Field Guide, in particular the detailed guidance in Filming Secure Scenes and Adding Essential Information to Video.
How anonymous is the data?
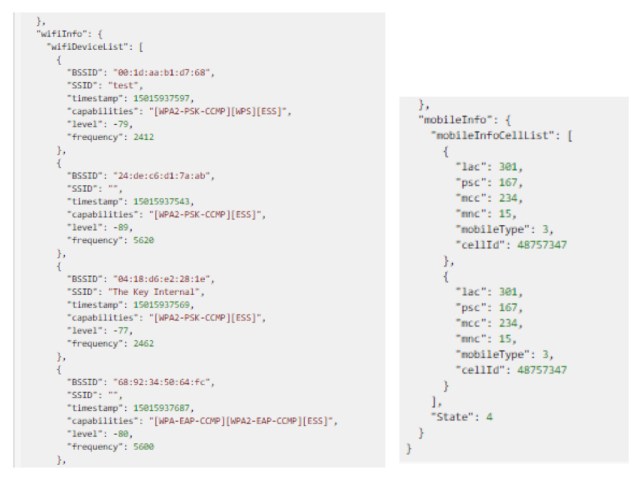
It is also important to know what metadata is being collected if you wish to remain anonymous or at least keep certain data private. For instance, some apps may collect the IP address from where you are when you upload the photo. This information can be used to trace your location. Only service providers will know the name of the owner of that IP address, but they can be compelled by law enforcement to produce that information. The important thing to keep in mind if you are sending your media to a third party and don’t want other people to identify you or your safe location, is some metadata, such as upload IP address, can give away that location.
WITNESS tip: Before you start using a documentation app, check what metadata the app captures. You can find this information in the metadata shown in the app, by reading the privacy policy, checking the app FAQs, or contacting directly the organization or developers. If the metadata includes information you do not want to reveal, consider using documentation apps that don’t capture that metadata.
How understandable is the data?
Finally, your metadata will not be very helpful if you or the final recipient cannot interpret it. For example, while many apps capture information on cell towers, you may be able to download or access only the raw metadata they capture. The Location Area Code (LAC), Mobile Country Code (MCC), Mobile Network Codes (MNC) and Cell Tower ID (CID), can help locate cell towers near where the footage was taken, but on their own they do not provide location information, only a set of numbers. Translating them into a location on a map requires either software or access to a database that will look up that raw data and transform it into a GPS location.
WITNESS tip: Consider what metadata you or your intended users (be they media outlets, policymakers, investigators, or other activists) need, and check whether your app captures that information in ways that both you and them are able to interpret and use.
The next post of the series will explain the limitations your metadata may have if you want to use it for legal purposes.
